The npm blog has been discontinued.
Updates from the npm team are now published on the GitHub Blog and the GitHub Changelog.
Two-factor authentication protection for packages
I’m happy to announce that you can now beta-test two-factor authentication protection for individual packages in the npm Registry. This setting requires that every publication of a protected package be authorized by a one-time password. This requirement is enforced even if maintainers of that package haven’t required two-factor auth for publication themselves—they’ll still be prompted for a code for this package. If a maintainer hasn’t enabled two-factor auth at all, they’ll be unable to publish the package until they do.
You can test this feature using the npm canary client, npmc. We recommend you invoke the canary using npx: `npx npmc`. You can also install the canary build of npm directly by running npm install -g npmc@latest.
Toggle the settings with these commands:
npx npmc access 2fa-required <package>
npx npmc access 2fa-not-required <package>
Or cd to your package directory then run npmc access 2fa-required. If you have two-factor auth enabled for package publication already, you’ll be asked to provide a one-time password. You will be prompted for a one-time password for all changes to that package from then on. This includes maintainer changes.
Here’s an example of enabling it for a package, then attempting to publish without an OTP:
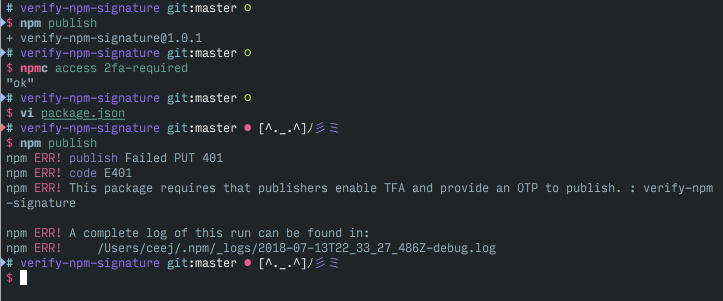
This setting isn’t visible in our web site yet, and support for toggling this setting isn’t in the default npm client yet. The default npm client behaves correctly when it encounters the setting, however, and will prompt for a one-time password when one is needed.
We will be encouraging maintainers of all popular packages to enable this to protect themselves and their users.