The npm blog has been discontinued.
Updates from the npm team are now published on the GitHub Blog and the GitHub Changelog.
Protecting Package Publishers: npm Token Security and Hygiene now Extend to GitHub
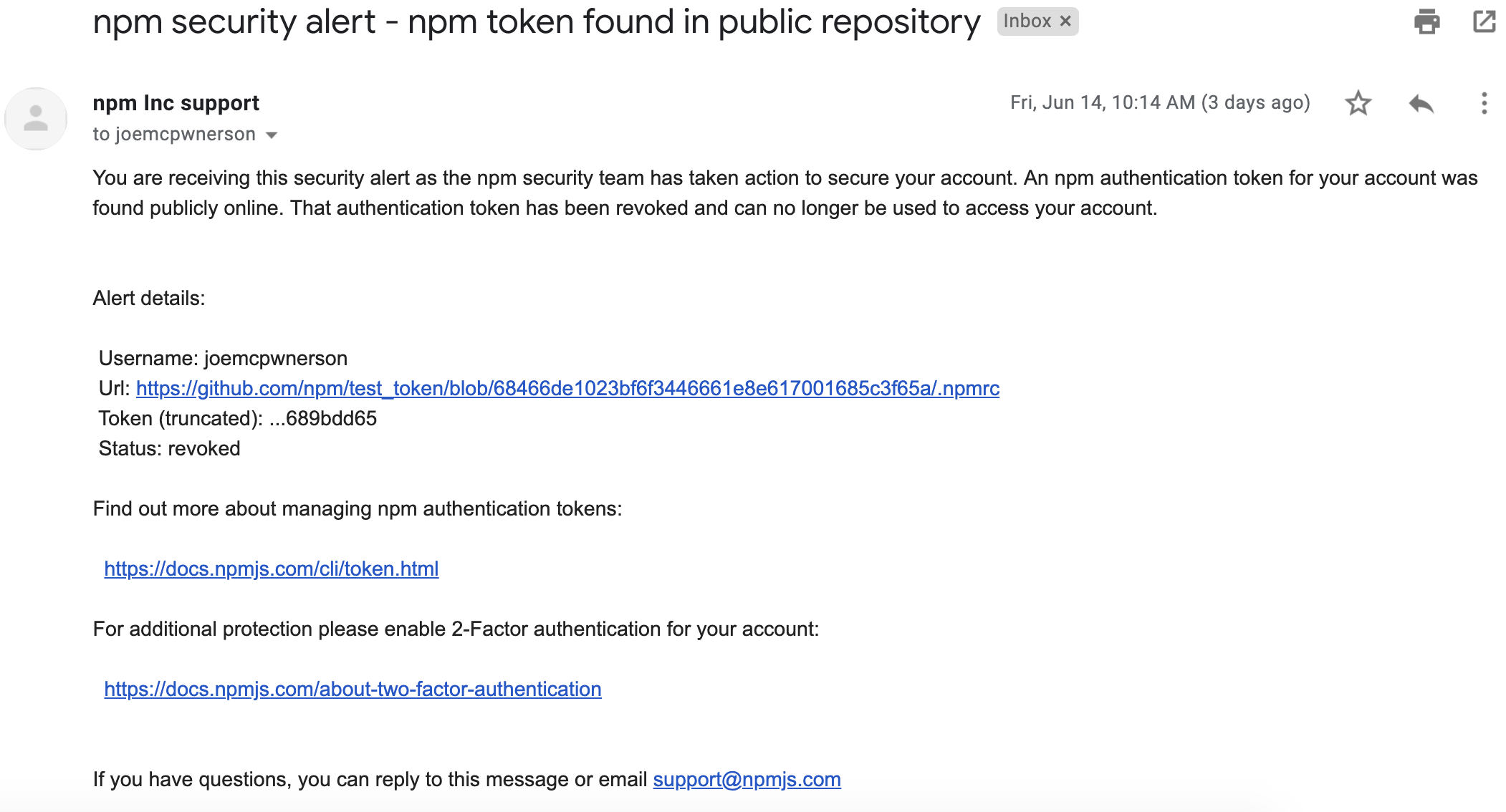
Today, we’re excited to announce that, in collaboration with GitHub’s token scanning partnership program, we’ve taken our existing token revocation efforts a step further. Whenever you commit or push a change to GitHub in a public repository and an npm token is found in the change, it is sent to npm for validation. If it’s valid, we will revoke it and notify the maintainer of this action via email.
npm maintainers are the foundation of the JavaScript supply chain. Compromising a popular maintainer’s npm account and publishing a new malicious package could have a lot of impact across the npm ecosystem. Not only that, but gaining access to a user’s account could give access to private packages and intellectual property. This is why all of us here at npm, Inc. focus a significant portion of our security efforts into protecting user accounts and credentials.
“Security is all about defense-in-depth; we’re very excited to have npm join us in the token scanning partnership program because it’s one of the best ways we can protect our mutual customers from account hijack and malware in software dependencies,” said Justin Hutchings, Senior Product Manager - Security at GitHub.
How you can keep your account and packages safe
First, you can enable 2-Factor Authentication for your account. This means that when you log into the website or publish a package using a token that was setup for ‘auth and publish’, a second factor is required to permit this action.
Second, if you maintain a package with multiple maintainers, you can require that 2FA be enabled to publish a package.
Finally, you can take steps to make sure you don’t accidentally publish sensitive configuration files by adding those sensitive files to your .gitignore and by using the files feature of package.json. This feature allows you to create a list of files you want to include in the published package.
Learn more in our upcoming JavaScript Supply Chain Security webinar.
About the npm Security Team
The safety and security of the npm public registry is critical to the JavaScript community at large and all of the applications that depend on it. While the primary defense against bad actors and malicious code has always been and will always be policing by the community itself, npm, Inc., as operator of the registry, has a unique role with valuable insights into security threats and code vulnerabilities.
As an additional layer of defense, we employ a dedicated security team staffed by the foremost experts in JavaScript security. Their continuous research and 24/7 vigilance is capable of detecting potential vulnerabilities the moment they are published and taking swift action to alert the community to potential risks and providing mitigation strategies before downstream users and customers are compromised.
We embrace opportunities to work with partners like GitHub to implement preventative measures and best practices that make the entire JavaScript ecosystem stronger and safer.